POSTS
🚀low latency firewall
By Philip
introduction
Since my last endavour in low latency firewalling, a lot has happend in the linux networking world. New algorithms where developed that reduce manual configuration by a large factor.
I use this setup at home to:
- keep gaming latency low
- keep voice call’s (teams, slack, discord, teamspeak) latency low
even in the event that there is high upload (cloud sync, email with large attachment, video streaming, backup), response times for interactive traffic are low and usable.
This article assumes you have a working linux based firewall with masquerading. The scope is only the low latency part!
In the article we use eth0 as internet interface. You need to replace it with your own internet facing adapter!
setup
I have an dsl line with only ~3,7Mbit upload. Wich isn’t very fast. I use a raspberry pi4 to act as a router/firewall.
Here is an network diagram:
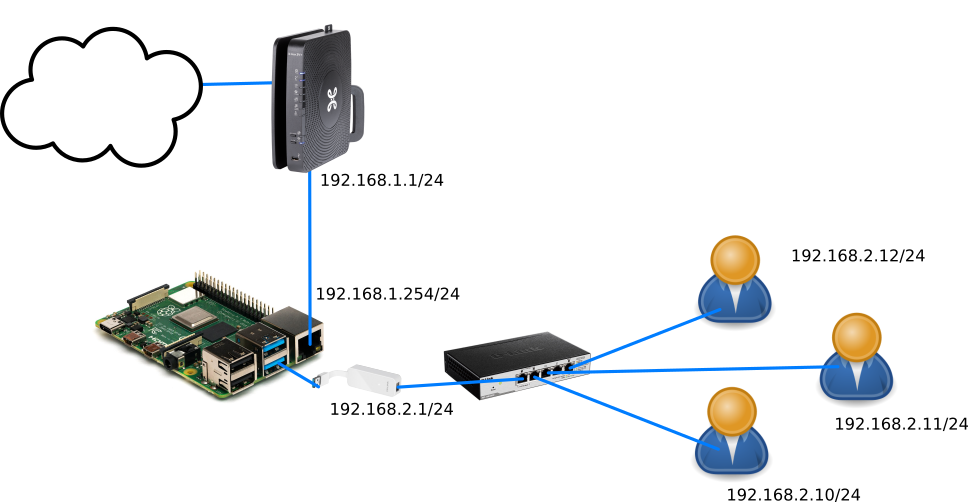
- eth0 is the internet interface
- eth1 is the lan interface
firewall (iptables, nftables, dhcp, dns, wifi, …) config and ip adresses are not in the scope of this post.
shaping config
install
To install the required scripts you need to execute the following commands:
# as root:
cd
git clone https://github.com/tohojo/sqm-scripts.git
cd sqm-scripts/
make install
that’s it, quite simple. The requered scripts are now installed.
baseline
before we create a config, you need to create a baseline bandwidth profile. (you need to know the upload and download speed of you internet provider). Try to minimize other internet traffix: no video streaming, gaming, … while you are testing the speed. Best is to disconnect everything besides the test workstation.
Testing is done with dslreports.
Go to dslreports and select your internet technology you use. In my case “DSL”.
My result was:
- upload: 3,8 Mbit
- download: 43,2 Mbit
There are some speedtest score’s on the page, your’s probably wont be an A. But rather a B or lower
(you can do the speedtest multiple times and take an average) DSL speed’s can vary so it’s better to be on the safe side, so we take 80% instead of the default 90%:
- upload: 3,2 Mbit
- download: 36 Mbit
config
now create a configuration file:
# copy the default config, the internet interface is eth0
cp /etc/sqm/default.conf /etc/sqm/eth0.iface.conf
# edit to input the correct options
nano /etc/sqm/eth0.iface.conf
now it’s time to input the correct variables:
# enable this config, otherwise no shaping wil take place
ENABLED=1
# Uplink and Downlink values are in kbps
UPLINK=3200
DOWNLINK=36000
# SQM recipe to use. For more information, see /usr/lib/sqm/*.help
SCRIPT=piece_of_cake.qos
# DSL line's have some per packet overhead,
# sqm wil compensate for this with the following option:
# this is not nessecery for cable of ethernet connectivity.
#the manpage of tc-cake list the available options
LINKLAYER=atm
# Extra qdisc options ingress resp. egress
# this is a masqing firewall (nat),
# an extra option to further optimize shaping:
IQDISC_OPTS="nat"
EQDISC_OPTS="nat"
well then, everything is in place to start shaping:
# as root:
sqm start
if everything goes well the output will be:
Starting SQM on all configured interfaces.
Stopping SQM on eth0
Starting SQM script: piece_of_cake.qos on eth0, in: 36000 Kbps, out: 3200 Kbps
piece_of_cake.qos was started on eth0 successfully
thats it! You just configured a “smart queue management” firewall. The sqm script is executed every time you reboot or when you hotplug a netwerk adapter.
test again
to see the difference, you should run a new test with dslreports You are supposed to get A or A+ on all the scores.
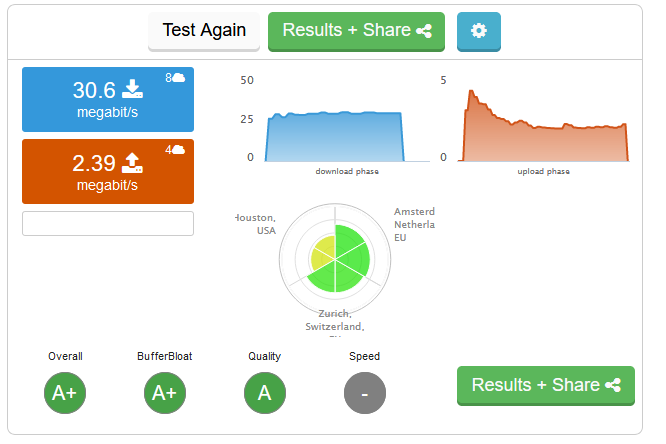
succes! 🥳🎈
checking
to check if sqm is working you can use the folling commands:
tc qdisc show
will give:
qdisc cake 802a: dev eth0 root refcnt 2 bandwidth 3200Kbit besteffort triple-isolate nat nowash split-gso rtt 100.0ms atm overhead 0
qdisc ingress ffff: dev eth0 parent ffff:fff1 ----------------
qdisc cake 802b: dev ifb4eth0 root refcnt 2 bandwidth 36Mbit besteffort triple-isolate nat wash split-gso rtt 100.0ms atm overhead 0
this will show your eth0 interface with:
- qdisc cake: cake is the algorithm that does the hard work of shaping,queuing,… for the upload traffic
- the bandwith you configured in the config file
- the ifb4eth0 is an ifb virtual adapter to manage the download traffic (shaping can only be done on outgoing traffic in linux)
even more info
tc -s qdisc show
references
man tc-cake- https://openwrt.org/docs/guide-user/network/traffic-shaping/sqm-details#making_cake_sing_and_dance_on_a_tight_rope_without_a_safety_net_aka_advanced_features
- https://www.youtube.com/watch?v=LjJW_s5gQ9Y
- https://wiki.archlinux.org/index.php/advanced_traffic_control
- http://www.taht.net/~d/lca_tcp3.pdf
- https://gettys.wordpress.com/2018/02/11/the-blind-men-and-the-elephant/
bonus: simple nat setup with iptables
You can use these command’s to create a very simple masquerading firewall:
# enable forwarding
sysctl -w net.ipv4.ip_forward=1
# masq internet traffic
iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE